End-to-end Azure architecture
Final Weather Tracker architecture showing GitHub Actions, Docker, ACR, Container Apps, Azure Monitor, and Key Vault.
This project started as a local FastAPI weather application and evolved into a production-style Azure platform. It uses Docker, Azure Container Registry, Azure Container Apps, structured logging, Application Insights, Azure Monitor alerts, GitHub Actions CI/CD, and Azure Key Vault with managed identity.
GitHub push → GitHub Actions → Docker build → Azure Container Registry → Azure Container Apps → FastAPI Weather App → WeatherAPI → Structured logs → Application Insights → Azure Monitor alert → Action Group email → Key Vault secret via managed identity
This project demonstrates how a simple application can be engineered into a secure, observable, containerized Azure workload. The final architecture keeps the project focused: FastAPI Weather App → Structured Logging → Azure Monitor + Alerts → Docker → ACR → ACI validation → Azure Container Apps → GitHub Actions CI/CD → Azure Key Vault.
A local FastAPI app is not enough for a serious cloud portfolio. This build turns the application into a deployable service with runtime configuration, cloud monitoring, container packaging, automated deployment, and secret management.
The final runtime uses Container Apps as the live platform, ACR as the image source, GitHub Actions for CI/CD, Azure Monitor for operational visibility, and Key Vault with managed identity for the WeatherAPI secret.
The project intentionally avoids being just a weather UI. The strongest parts are the operational and security layers.
The final platform follows a realistic cloud delivery path: application code is committed to GitHub, GitHub Actions builds a Docker image, the image is pushed to ACR, and Azure Container Apps runs the container with managed ingress and Key Vault-backed configuration.
All screenshots included below are packaged inside this folder under images/. Click any card to open the full screenshot.
Final Weather Tracker architecture showing GitHub Actions, Docker, ACR, Container Apps, Azure Monitor, and Key Vault.
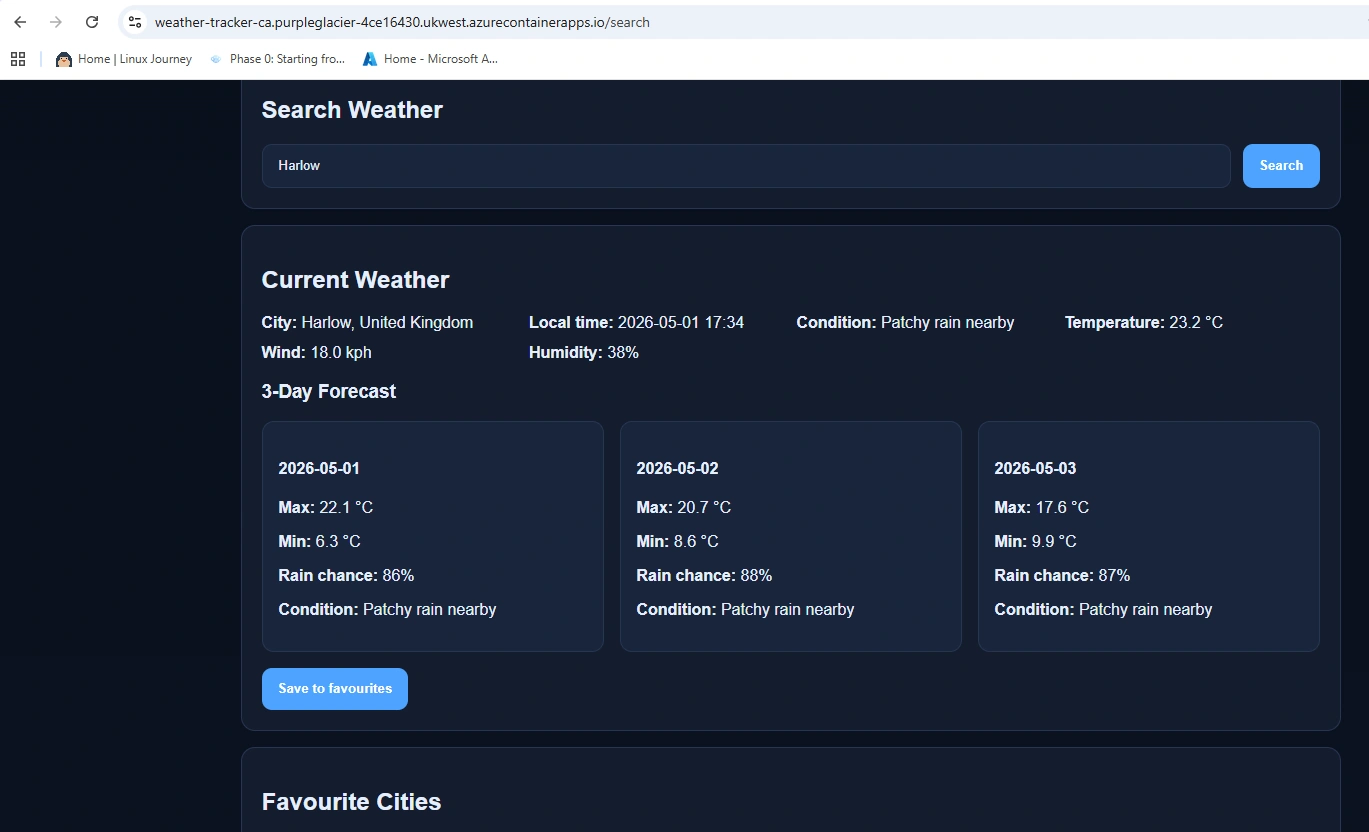
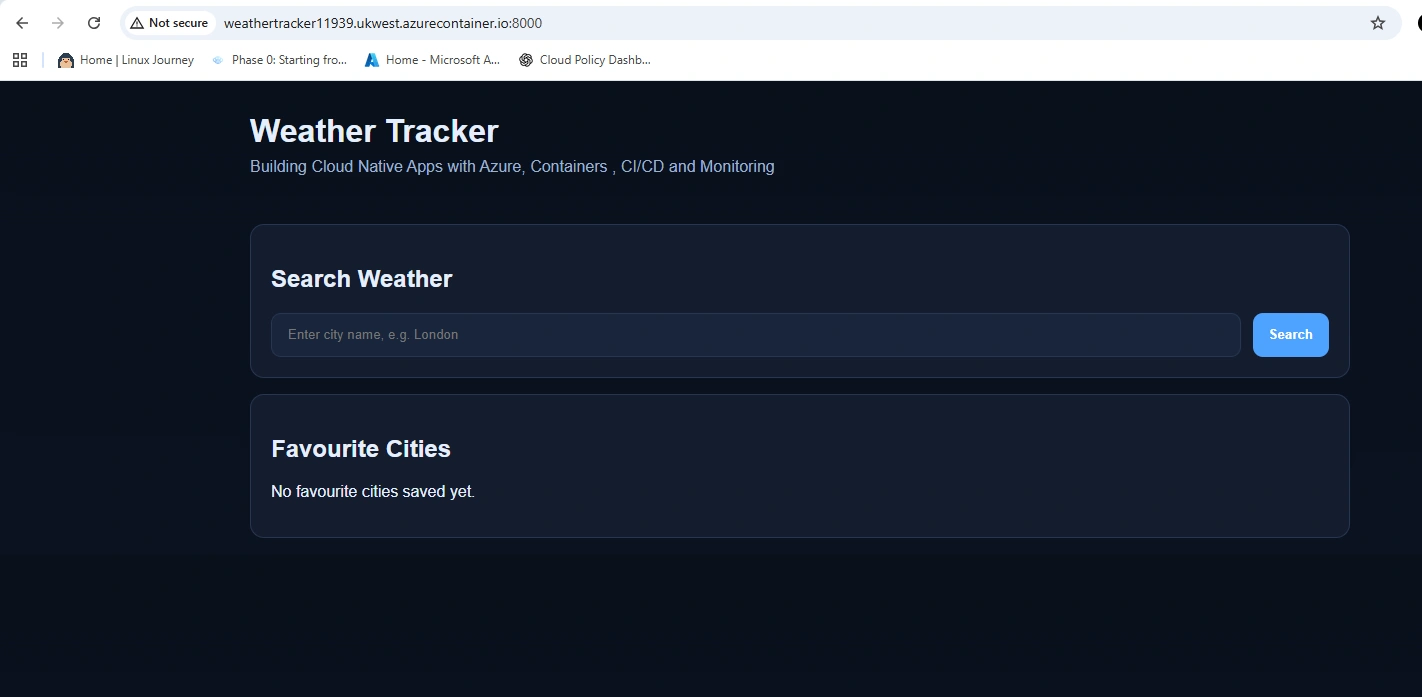
Weather search working from the public HTTPS Container Apps endpoint.
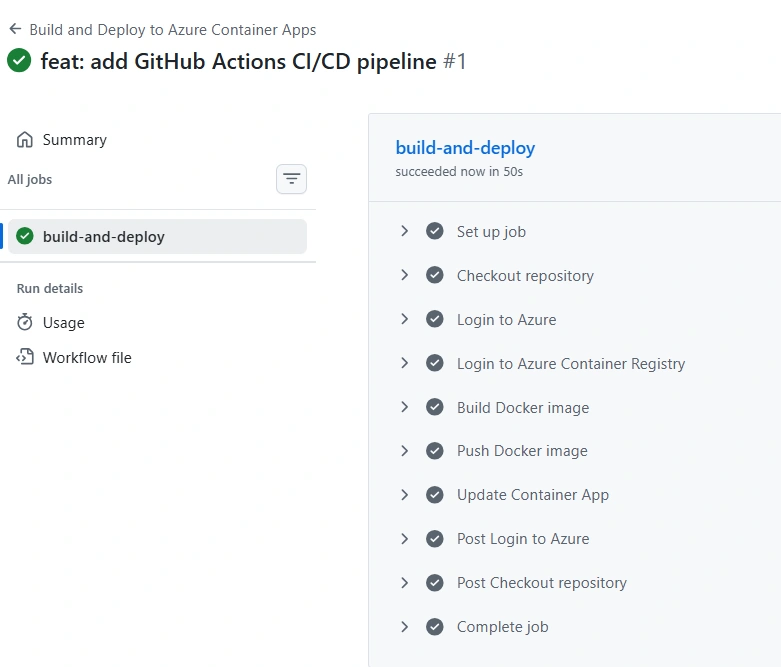
GitHub Actions built the Docker image, pushed to ACR, and updated Container Apps successfully.
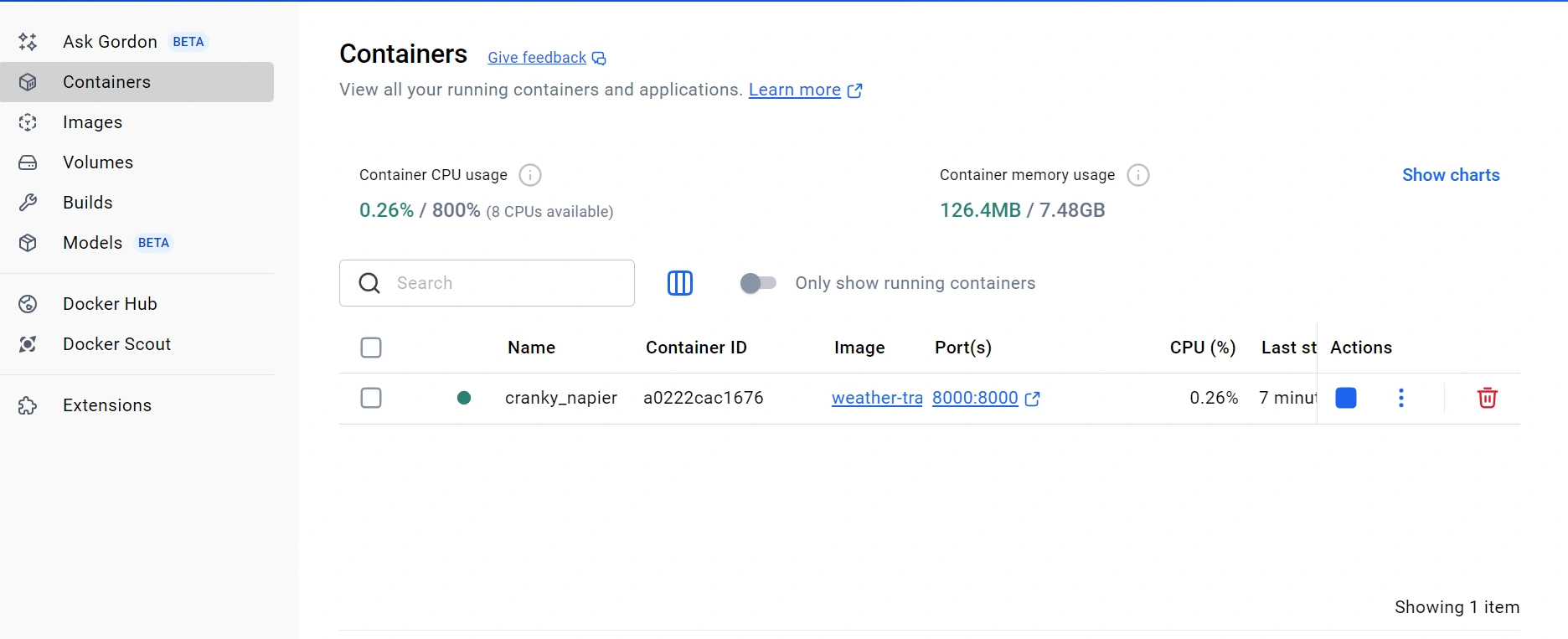
Local container running with Docker Desktop before cloud deployment.
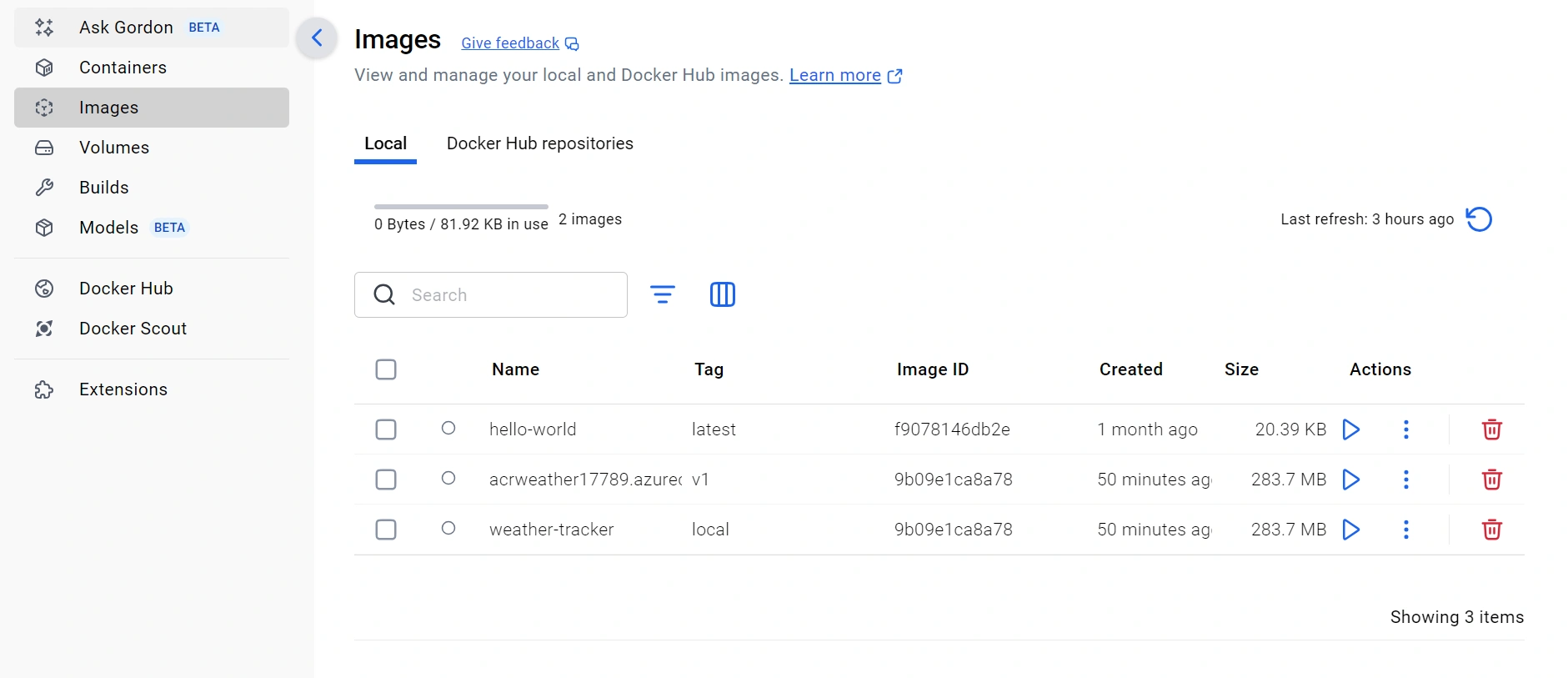
Local Docker image and tagged ACR image ready for push.
Short-lived ACI validation proving the ACR image runs in Azure.
Weather Tracker running locally from the Docker container.

Earlier App Service deployment validating the web app before container production runtime.
Application Insights request records for live application traffic.
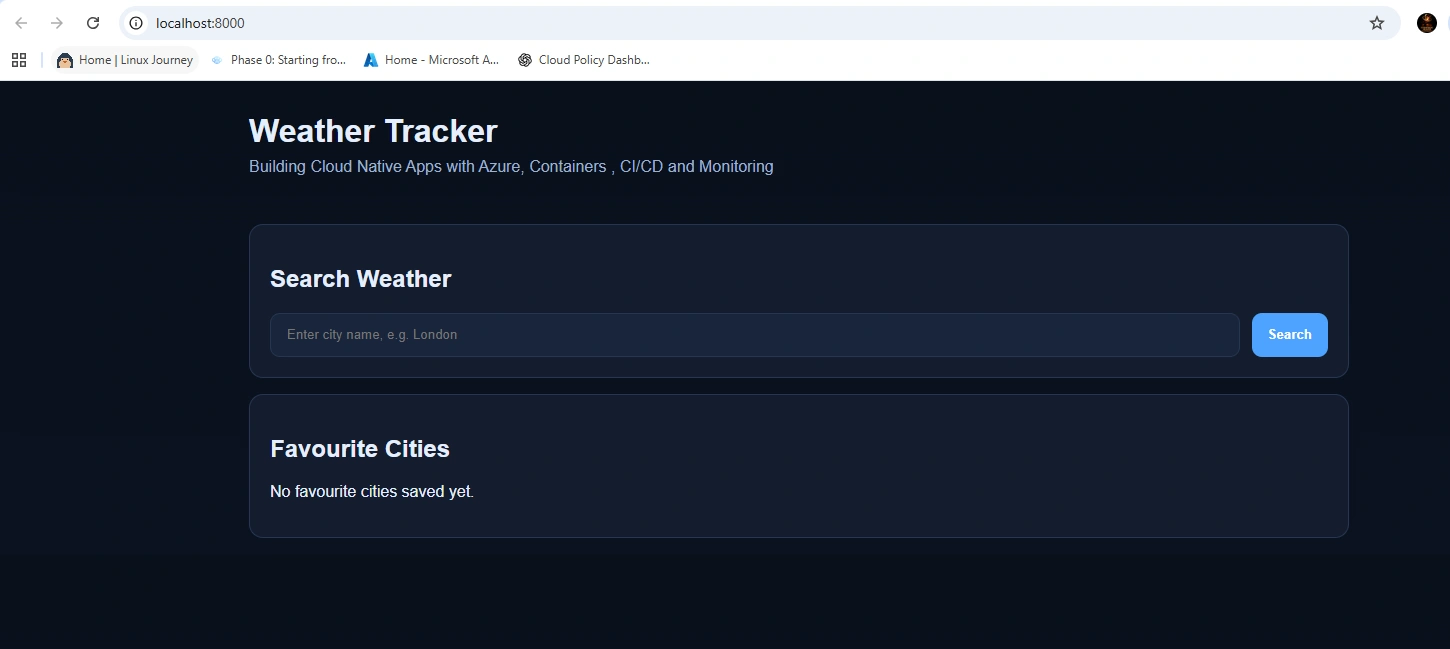
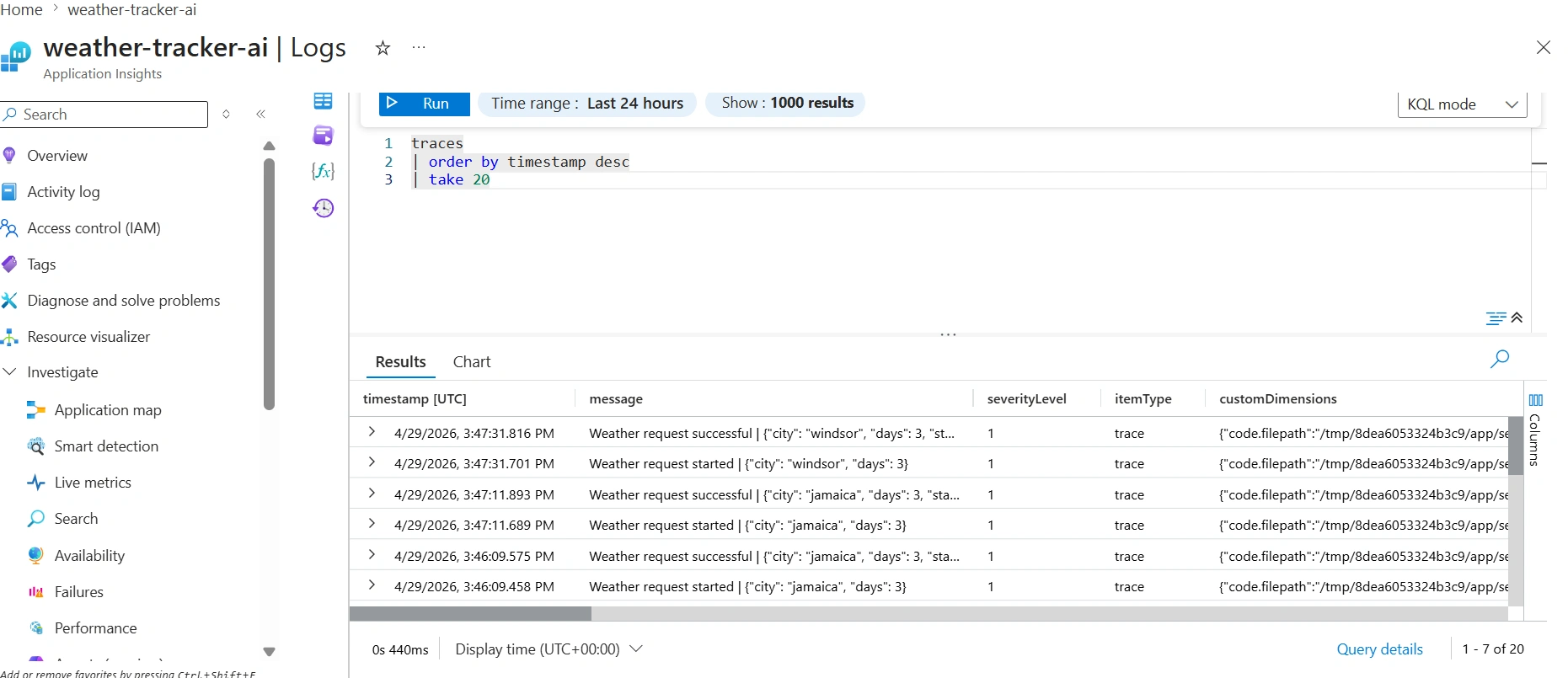
Structured weather request logs showing city, result, and context.
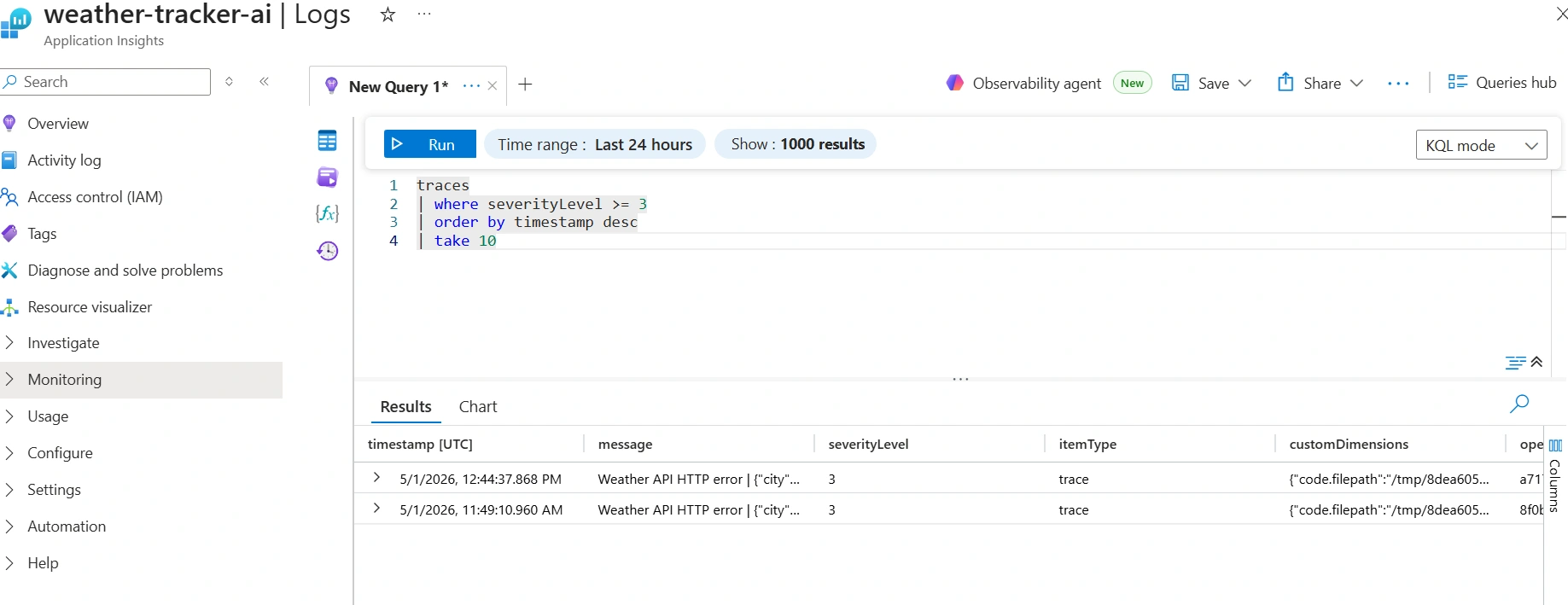
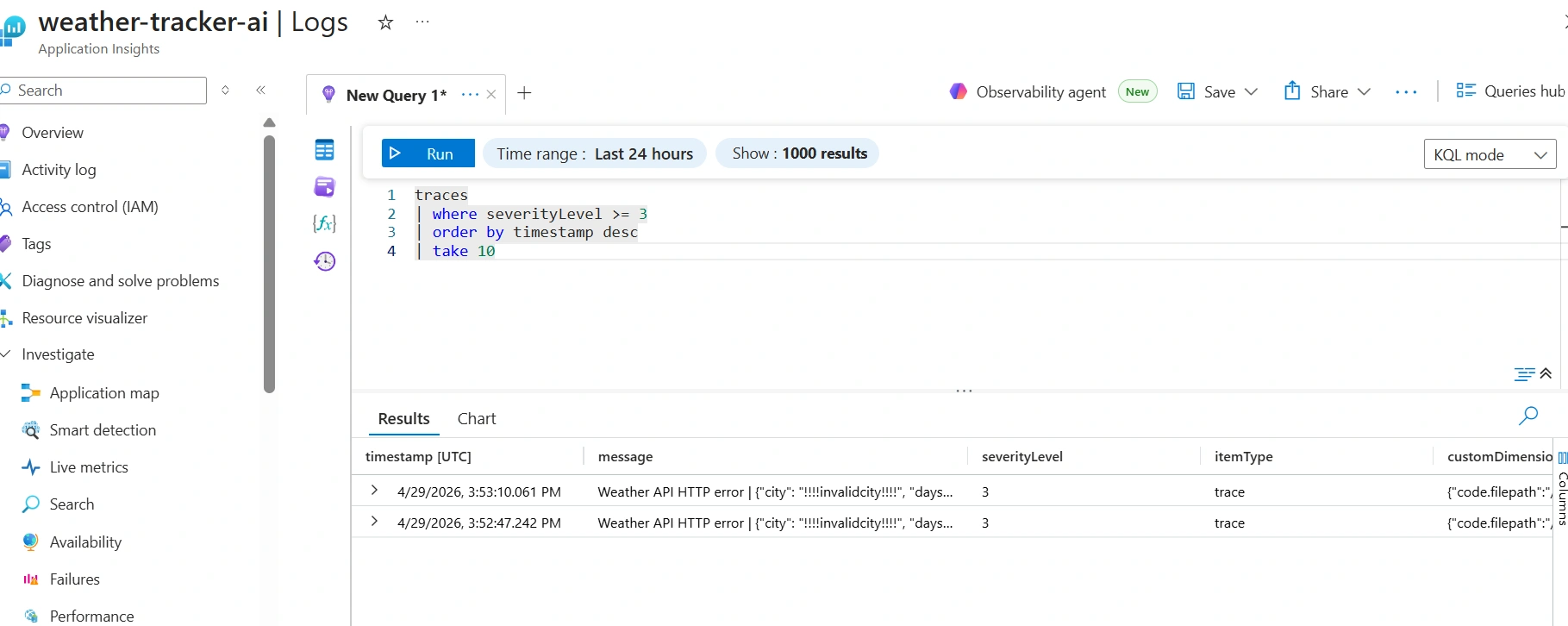
KQL trace results showing Weather API HTTP errors used for alerting.
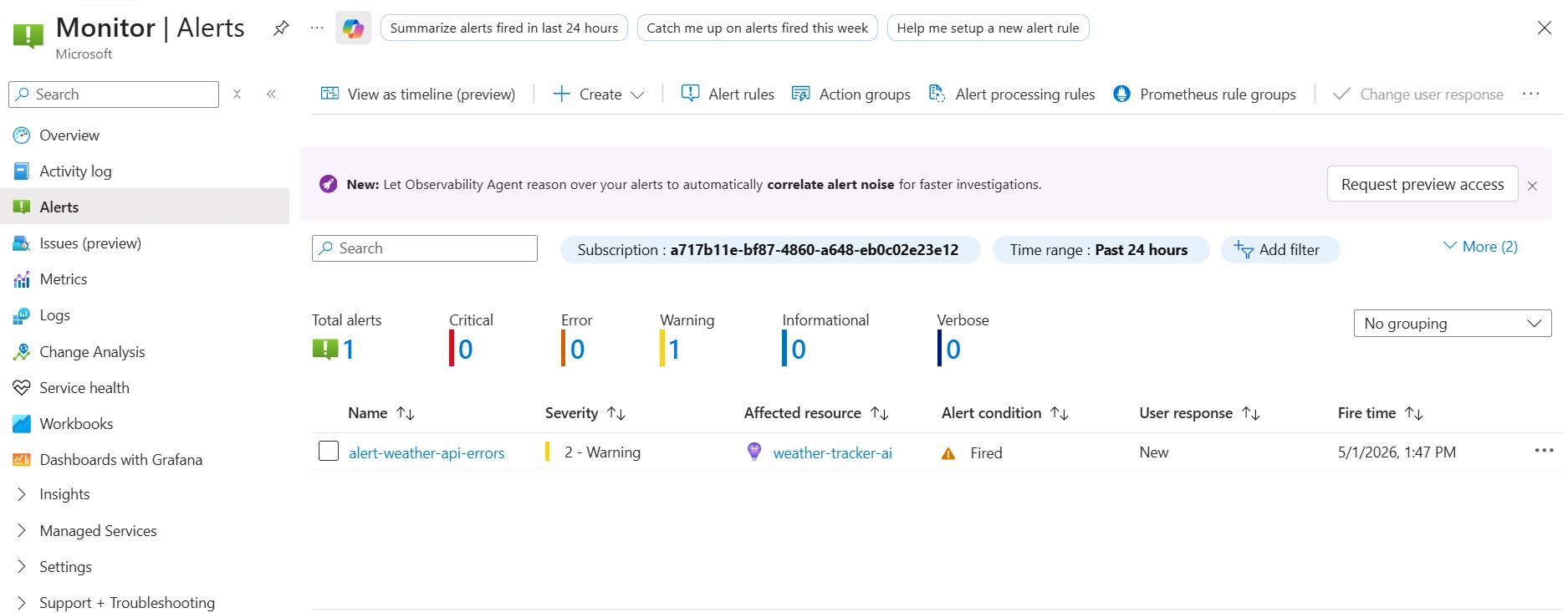
Azure Monitor fired the weather API error alert when the threshold was crossed.
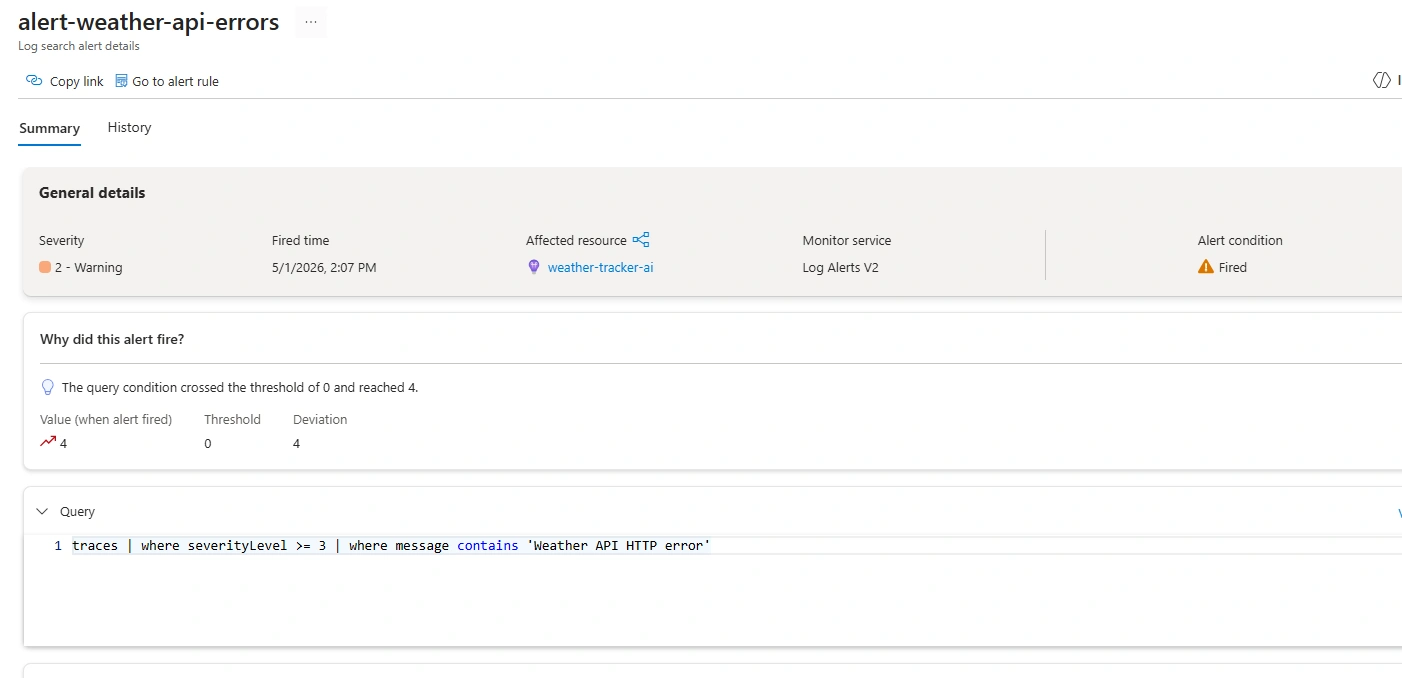
Azure alert details showing query, threshold, and fired condition.
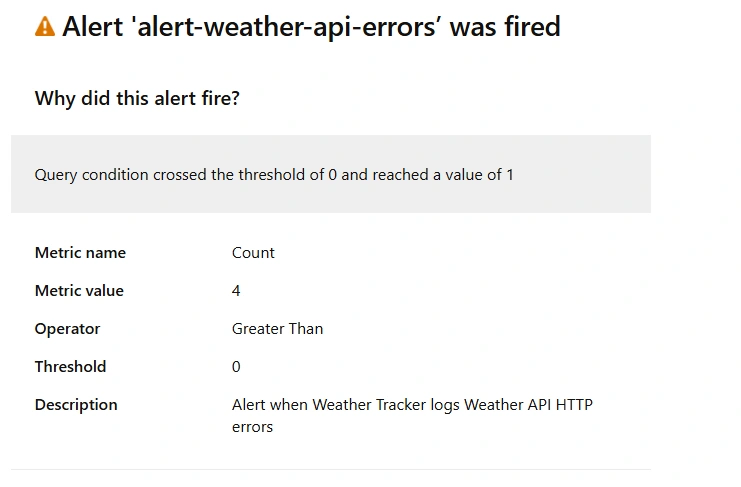
Email notification from Azure Monitor proving the alert action group worked.
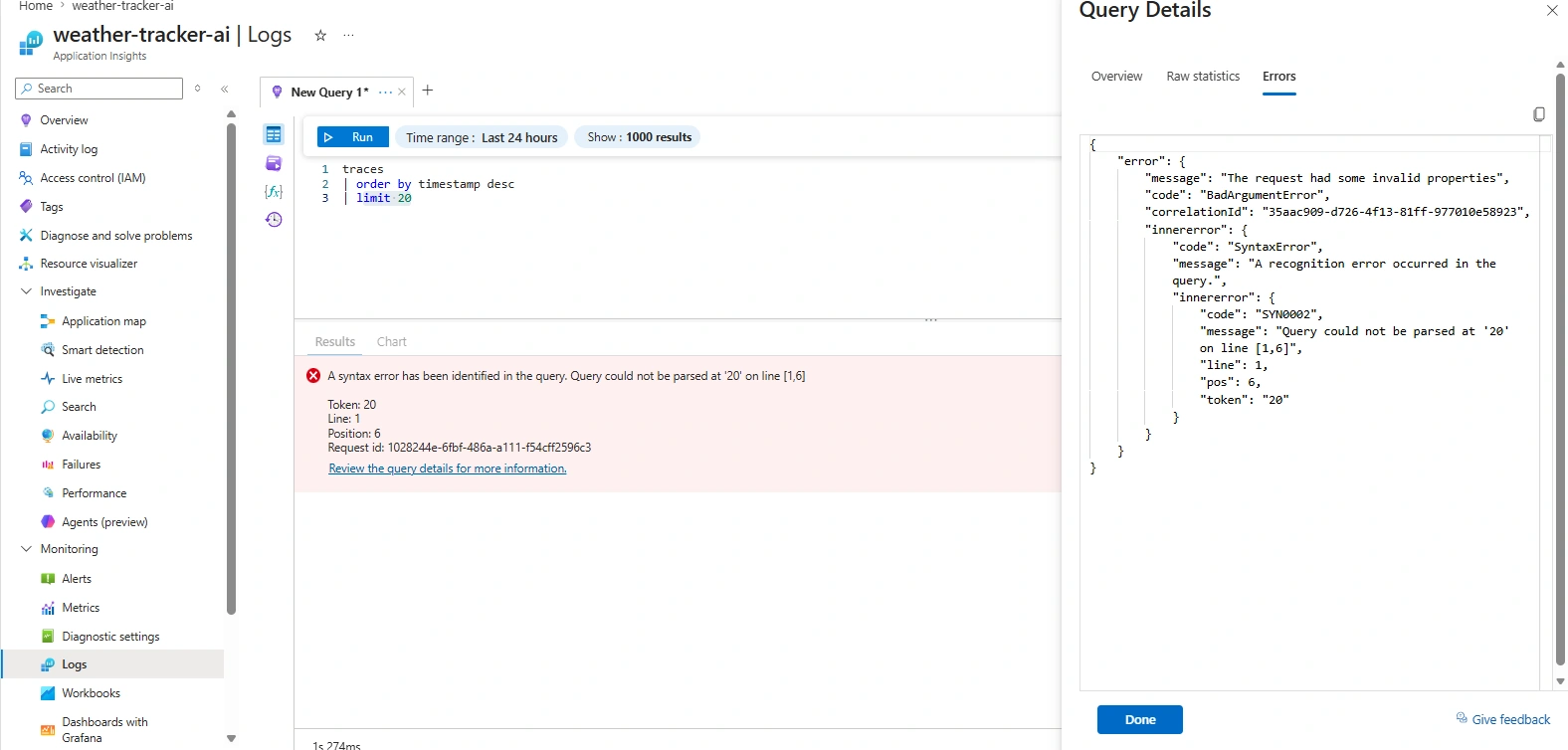
A real scheduled query/KQL syntax issue encountered and fixed during alert creation.
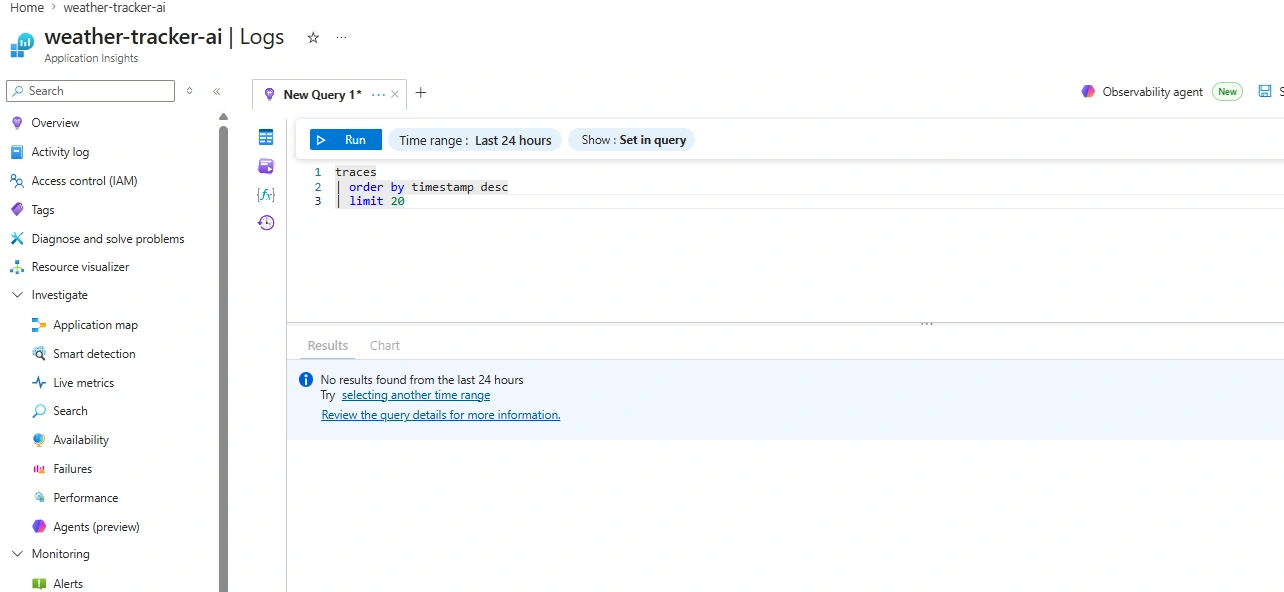
Early Application Insights query returning no traces before instrumentation was corrected.
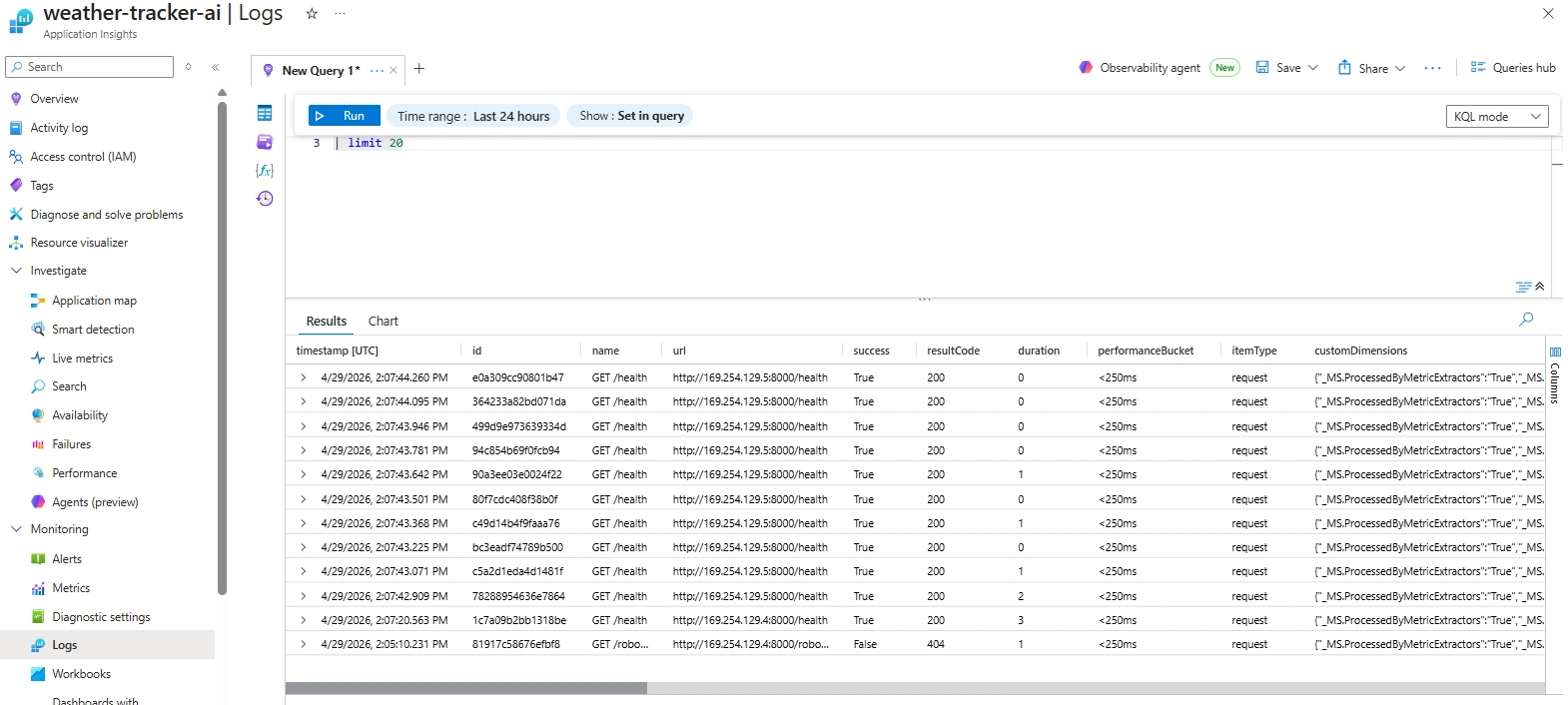
Application Insights requests table populated after telemetry started flowing.
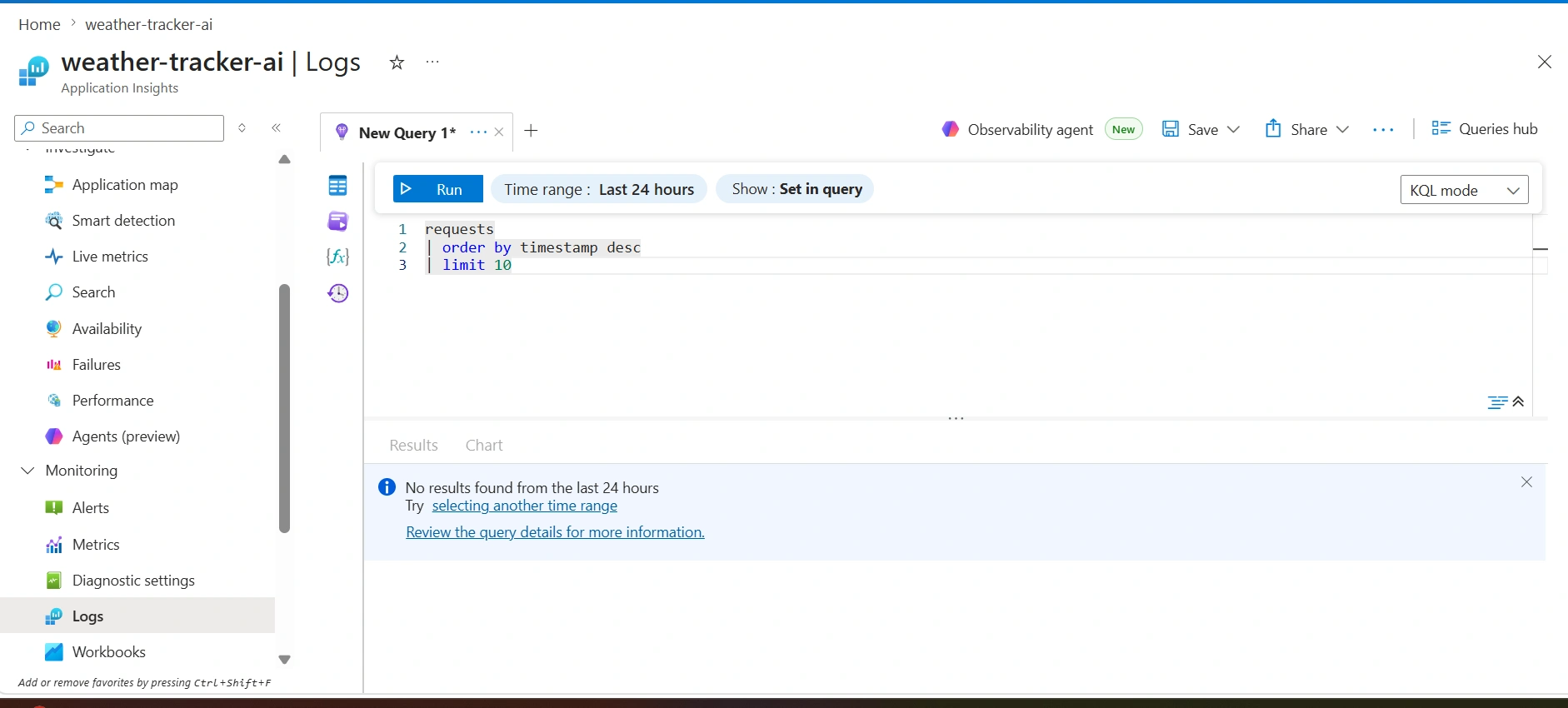
One of the early telemetry validation screens before logs appeared correctly.
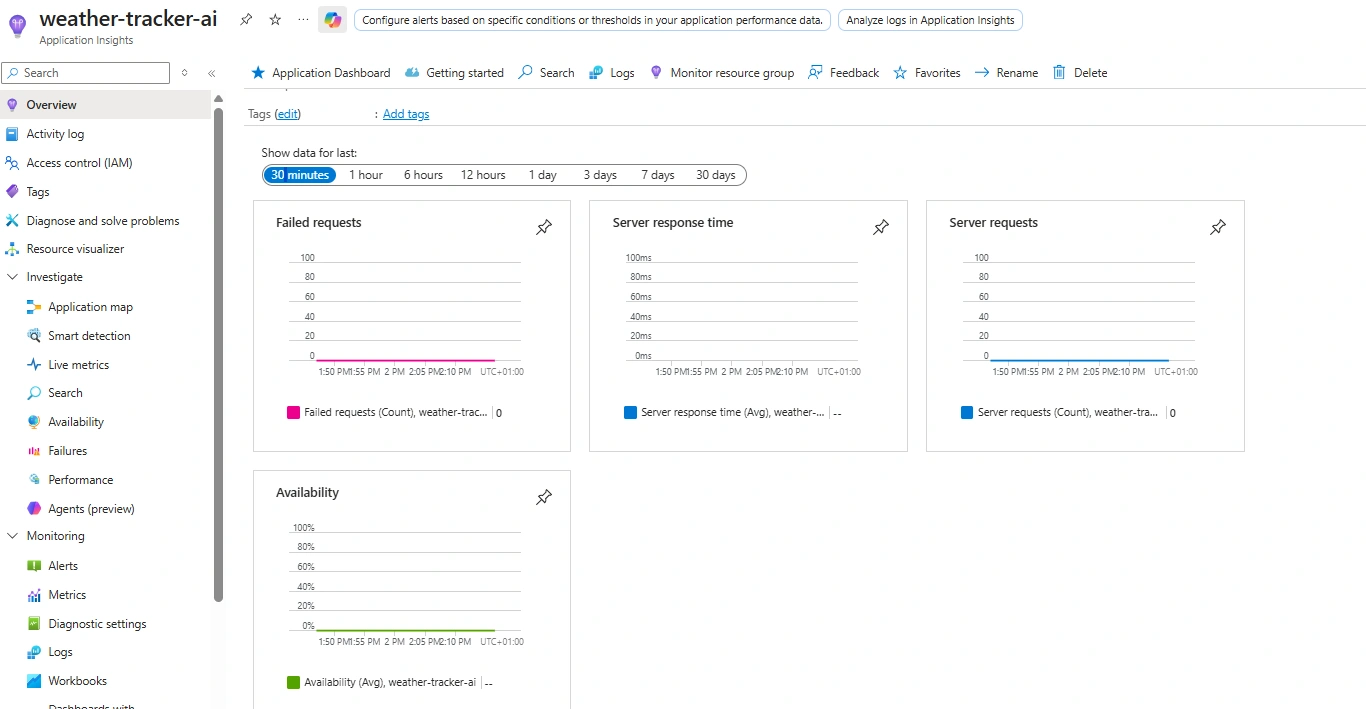
Application Insights overview used during monitoring validation.
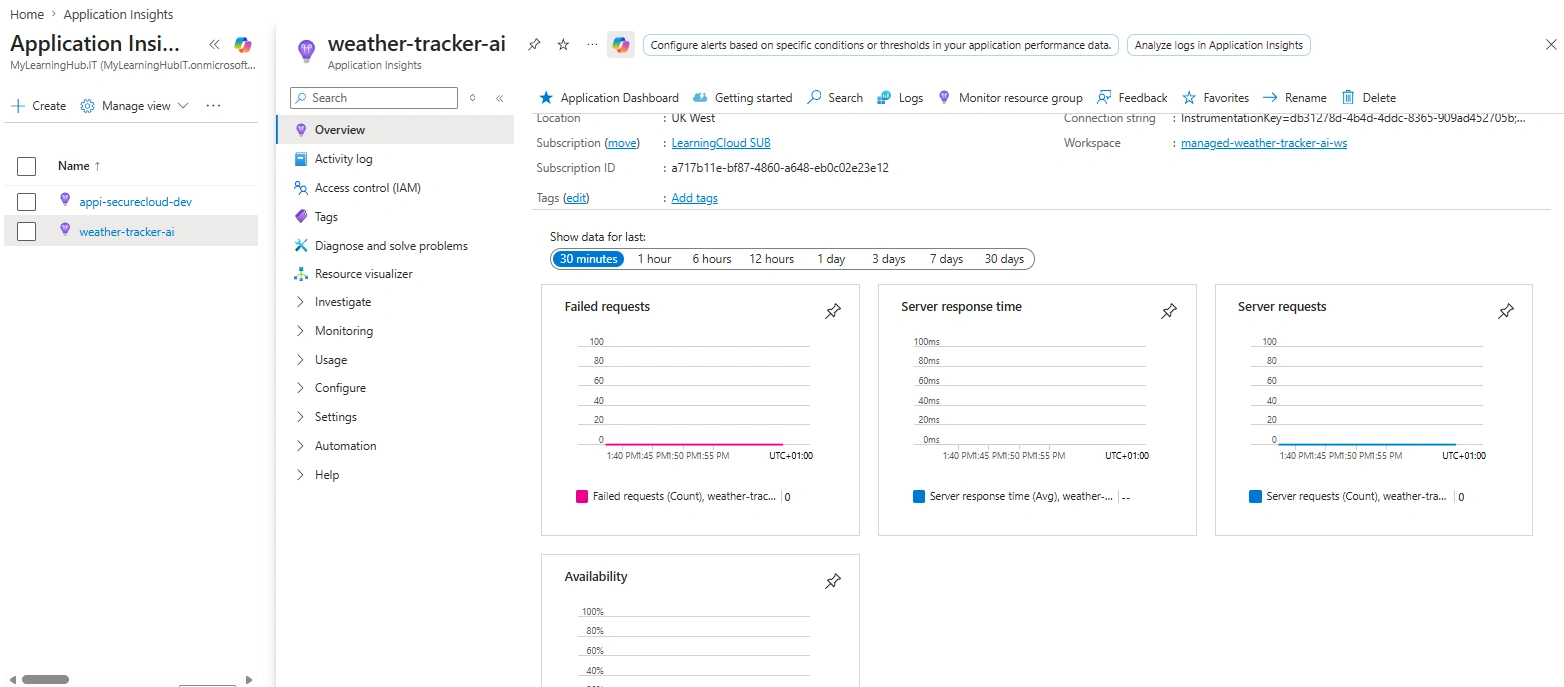
Azure metrics dashboard evidence from the monitoring stage.
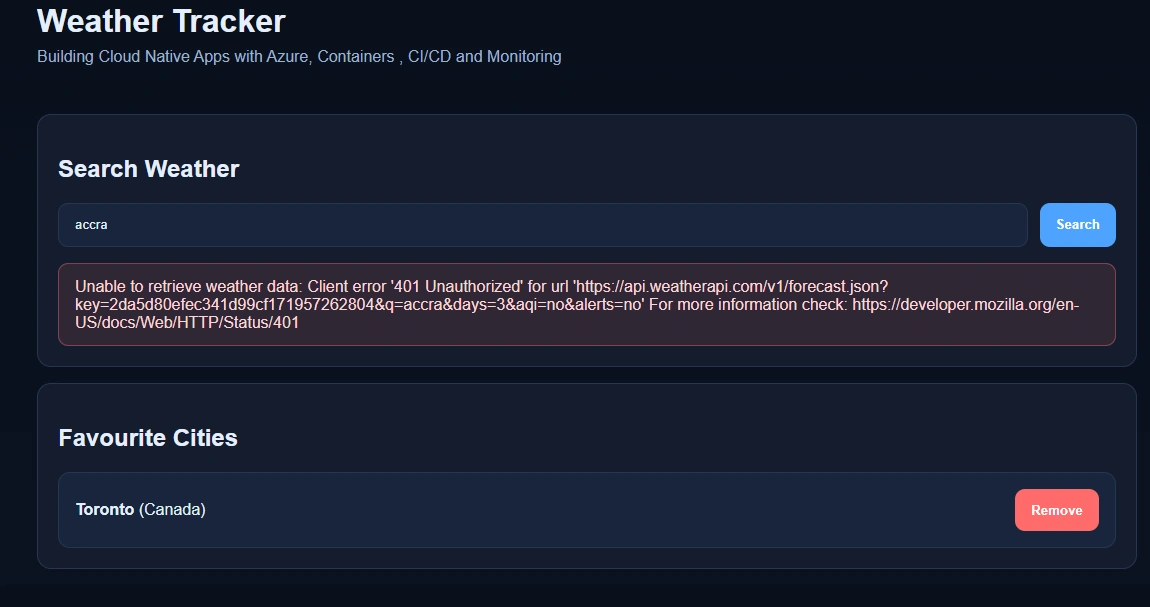
Early local WeatherAPI 401 issue, later fixed by correct API key/environment configuration.
The validation flow proves the app works at every stage: local runtime, Azure App Service, telemetry, Docker, ACR, ACI, Container Apps, CI/CD, and Key Vault-backed secret delivery.
Created a FastAPI app with city search, forecast display, favourites, and a health endpoint.
Validated cloud hosting with Azure App Service, environment variables, and Gunicorn startup.
Integrated Application Insights and validated requests, traces, errors, and KQL queries.
Created Azure Monitor alert rules and Action Group email notifications for Weather API failures.
Created Dockerfile and .dockerignore, then tested the container locally with environment injection.
Tagged and pushed the container image to Azure Container Registry.
Ran the image in Azure Container Instances as a short-lived validation runtime, then deleted it for cost control.
Created a Container Apps environment and deployed the app with public HTTPS ingress and scale-to-zero.
Configured CI/CD to build Docker images, push to ACR, and update Container Apps on every push.
Stored the WeatherAPI key in Key Vault and connected it to Container Apps using managed identity.
The stack is deliberately focused on Azure Cloud Engineer skills: compute hosting, containers, monitoring, CI/CD, and secret management.
A production-style Azure workload demonstrating FastAPI hosting, structured logging, monitoring, Docker, ACR, ACI validation, Container Apps, GitHub Actions, and Key Vault-backed secret management.
The strongest learning came from real Azure errors: quota limits, startup dependency issues, telemetry gaps, CLI syntax differences, ACI crash loops, port mapping quirks, and RBAC permissions for Key Vault.
The FastAPI app had a production startup command using Gunicorn, but gunicorn was not in requirements.txt. Adding it fixed the App Service startup path.
gunicorn==23.0.0.The first monitoring setup created Application Insights but did not show useful FastAPI request telemetry. The fix was to use Azure Monitor OpenTelemetry and initialize it before the app fully loaded.
The scheduled query alert failed until the query placeholder syntax was corrected using a named condition query.
The local Docker container worked because it read .env, but the Azure CLI deployment needed the shell variable exported explicitly.
Creating the Key Vault with RBAC enabled did not automatically grant permission to set or read secrets. The fix was to assign Key Vault Secrets Officer to the user and Key Vault Secrets User to the Container App managed identity.